OTPulse Weekly Briefing - May 4, 2026
 Jerrid Brown·OTPulse
Jerrid Brown·OTPulseMoxa just patched a CVSS 8.7 unauthenticated DoS across six product families, including the OnCell LTE routers most utilities run at remote sites. The patch only fixes half the problem. Here is what to do for the other half, and why this is the third edge-device advisory in three weeks.
This week in OT security
Moxa published a security advisory on April 27 covering two CVEs across six product families: TN-4900 Series, EDR-8010 Series, EDR-G9010 Series, OnCell G4302-LTE4 Series, OnCell G4308-LTE4 Series, and EDF-G1002-BP Series. These are industrial routers and cellular gateways - the devices that connect a remote pump station or substation to the SCADA historian over LTE. CVE-2026-3868 is an unauthenticated remote DoS on the HTTPS management interface (CVSS 8.7). CVE-2026-3867 is a low-privilege password hash exposure via exported config files. Firmware v3.24 fixes the issue for most affected families. OnCell users specifically need to contact Moxa Technical Support to request v3.24.1 - it is not available through the standard firmware download path.
The patch is good news, but it does not eliminate the full risk picture. Most teams that manage remote Moxa routers have exported configuration files at some point, usually as part of a maintenance or backup workflow. Those files contain the admin password hash. If a low-privilege user has accessed a backup file before this patch, the hash is already exposed and patching does not undo that. The remediation section below covers what to do about existing backup files.
This is also the third edge-device advisory in three weeks. Two weeks ago: ArcaneDoor FXOS persistence on Cisco firewall hardware, state-sponsored, survives the application-layer patches. Last week: CISA and NCSC joint advisory on Chinese state-sponsored actors maintaining covert networks of hijacked SOHO routers and IoT devices. This week: Moxa secure routers, the devices that physically bridge your OT network to the outside world. The pattern is consistent enough to treat as a theme, not a coincidence. The edge device connecting your remote site is the current campaign's preferred first step.
Top 5 advisories to act on
CVSS 8.7 across six product families. Firmware v3.24 is available; OnCell families need v3.24.1 via Moxa support contact. Full breakdown below.
Carryover from last week. The FXOS-layer persistence mechanism survives the September 2025 ASA/FTD application patches intact. If your device was reachable before you applied those patches, verify FXOS integrity before considering the box clean - a version check on the application layer is not sufficient.
Wide product family: CHARX security controllers, AXC F industrial controllers, FL MGUARD firewalls, FL WLAN access points, and TC ROUTER cellular routers. Exploitation requires elevated credentials but the product scope is broad. Match the advisory against your Phoenix Contact inventory.
EPSS 41.6 percent is the highest exploitation probability in this week's OTPulse feed. Broken cryptography on industrial Ethernet switches means traffic can be decrypted by an attacker already on the segment. Fix: firmware V1.10.212 or later.
Full Milesight camera lineup affected, no authentication required. Milesight cameras are widely deployed at water and energy utility perimeter monitoring, often sitting on management VLANs with broader segment access than expected. If you have them on your network, treat this as an Act Now.
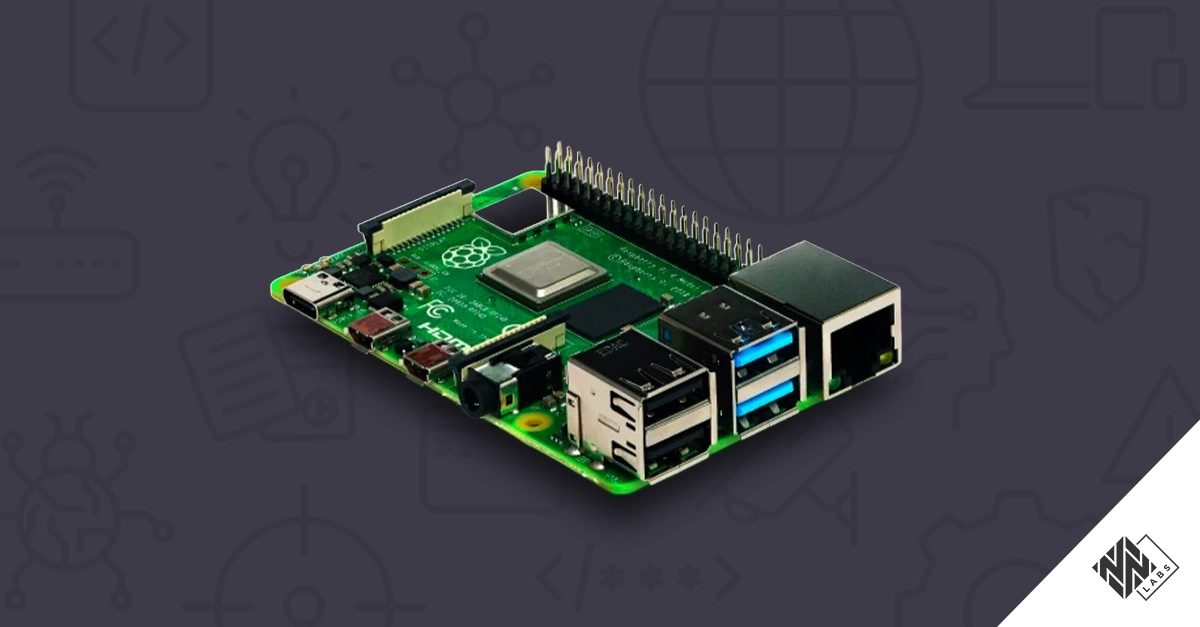
What Moxa Secure Routers actually do at your remote sites
The TN-4900 and EDR series are industrial secure routers designed for OT network segmentation and remote backhaul. At a pump station or substation, you typically find one sitting at the boundary: one interface connected to the OT network (PLC, RTU, flow meter), and one connected to a cellular WAN link that provides the remote path back to the SCADA historian. The OnCell G4302-LTE4 and G4308-LTE4 variants are the cellular-specific models - designed for sites where wireline connectivity is impractical, which describes most remote utility installations.
This dual role is what makes these devices high-value targets. If an attacker crashes the management interface, they disrupt your ability to manage the device remotely (forcing a truck roll to the site) and they may also use the disruption as cover for configuration changes that survive the reboot. If they extract the admin credential hash, they can attempt an offline crack and potentially own the router - which also means owning the remote access path to whatever is behind it.
The two CVEs side by side
| CVE | Type | Auth required | Condition | Impact |
|---|---|---|---|---|
| CVE-2026-3868 | Buffer overflow / DoS | None | Network access to HTTPS management port | Web service crashes, device reboot required |
| CVE-2026-3867 | Config file hash exposure | Low-privilege authenticated | Config file exported previously | Admin password hash readable, offline crack possible |
CVE-2026-3868 is the higher-urgency finding. No authentication, low complexity, remotely exploitable from any segment that can reach the management interface. A crash forces a reboot and a truck roll if you have no out-of-band management path. CVE-2026-3867 is lower urgency in isolation, but config exports are a standard ops practice - most teams have exported at least one config backup during commissioning or a maintenance window. If that file exists on a network share or in a maintenance laptop's Downloads folder, the condition for exploitation is already met.
What patching actually involves for these devices
Firmware v3.24 covers the TN-4900, EDR-8010, EDR-G9010, and EDF-G1002-BP families through the standard Moxa firmware download path. For OnCell G4302-LTE4 and OnCell G4308-LTE4, the patch version is v3.24.1 and it requires a direct support contact - you cannot download it from the Moxa website without opening a case. The Moxa advisory page for MPSA-261521 confirms this directly.
For remote pump stations and substations, the practical staging reality is that firmware updates often require a maintenance window scheduled weeks out. Until you can stage the patch, the compensating controls below are not optional - they are the actual mitigation plan.
Five things to do this week beyond patching
-
Restrict HTTPS management to a dedicated management VLAN. The management interface should not be reachable from the OT network segment or from the WAN interface. If you cannot isolate it today, adding a firewall ACL blocking port 443 inbound to Moxa device IPs from untrusted segments is the interim fix. Pull those ACLs now and verify.
-
Treat every config backup as a compromised secret. If your team has exported a configuration file from any of these devices - during commissioning, during a maintenance window, for disaster recovery documentation - that file contains the admin password hash. Locate all copies (USB drives in panels, network shares, maintenance laptops) and rotate the admin password before and after patching. The hash in the existing backup file is still crackable after you patch.
-
Set syslog alerting on router web service restarts outside maintenance windows. If Moxa devices are sending syslog to your SIEM, configure an alert on management service restarts that occur outside a scheduled window. An unexplained restart is the only outward sign you would notice of CVE-2026-3868 exploitation. If these devices are not sending syslog yet, configure it today - the management VLAN isolation step above makes this straightforward.
-
Open a Moxa support ticket for OnCell v3.24.1 this week. The lead time on vendor support contacts at remote utility sites is measured in days to weeks, not hours. If you have OnCell G4302-LTE4 or G4308-LTE4 devices in your environment, the support ticket needs to be open now. Do not wait until the maintenance window is scheduled.
-
Audit firewall rules for port 443 inbound to any Moxa management interface from an untrusted segment. Close those today. On most firewall platforms: pull the relevant ACL, filter for any allow rule that lists a Moxa device IP as the destination and 443 as the destination port, and confirm whether the source segment is trusted. On Cisco ASA:
show access-list | include 443and cross-reference against your Moxa device IPs.
Edge devices are the campaign
Three advisories in three weeks that share the same attack surface: the device connecting your remote OT site to the rest of the world. ArcaneDoor established FXOS-layer persistence on Cisco firewall hardware, specifically chosen because it survives application-layer patching. The China covert-network advisory documented active maintenance of compromised SOHO routers and IoT devices as covert infrastructure. Now Moxa secure routers, which handle cellular backhaul at remote utility sites, have an unauthenticated DoS and an admin credential exposure path.
The pattern is: identify the device that bridges the site network to central operations, develop or find a foothold there, and work inward from that position. Segmenting and monitoring edge devices - not just patching them - is the specific defensive requirement this campaign pattern demands.
GRASSMARLIN is end-of-life. If your team uses it, read this. CISA published ICSA-26-118-01 on April 28 covering CVE-2026-6807, an XML external entity injection in NSA GRASSMARLIN (CVSS 5.5, local access required). GRASSMARLIN was widely used by understaffed OT teams for passive network discovery, but NSA has archived the project and no patch is coming. If GRASSMARLIN is currently in your toolkit for OT network visibility, the actively-maintained replacement to evaluate is Malcolm - open source, maintained by CISA's NIWC Pacific team, designed for the same passive OT visibility use case, and explicitly recommended in CISA's new Zero Trust for OT guidance (see Industry Intel below) as an OT-protocol-aware open source SIEM. The advisory is at otpulse.io/feed/icsa-26-118-01.
Industry Intel
Reports & Research
Regulatory & Standards
Community
Get OT security insights every Tuesday
Advisory breakdowns, a weekly summary, and incident analyses for the people actually defending OT environments. Free, no account required.